The U.S. Army plans to deploy an authenticator app that will provide an alternative for personnel seeking to log into systems without a Common Access Card, FedScoop reported Monday. The Army is
MoreThe Department of Justice's (DOJ) Cybersecurity Unit has published a document that addresses the legality of certain intelligence-gathering approaches. The unit tackled methods that utilize online "dark web" forums where contributors discuss computer crimes and sell
MoreThe Department of Homeland Security's science and technology directorate partnered with the FBI to provide first responders with a water cannon technology designed to handle improvised explosive devices.
MoreThe National Science Foundation will invest $90 million in funds to support an initiative that seeks to develop a framework that will scale high-performance computing platforms and applications, HPCwire reported Monday.
MoreThe Government Accountability Office has found that while the National Nuclear Security Administration improved its management of weapons stockpile modernization efforts since 2003, it is yet to address challenges in cost and schedule management.
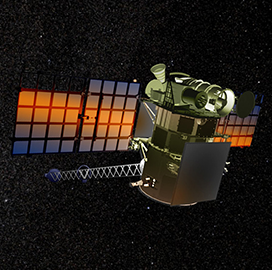
MoreThe National Oceanic and Atmospheric Administration worked with NASA to restore the Deep Space Climate Observatory or DSCOVR imagery satellite that went through some operational issues. NOAA said Monday it co-developed a flight
MoreAaron Weis, the U.S. Navy’s chief information officer and 2020 Wash100 Award winner, said the service’s networks are “holding us back” and exacerbating information leaks through the defense industrial base and direct exfiltration,
MorePivot3 has partnered with AIMES, a specialized cloud and data center service provider, to provide secure cloud-based trusted research environments (TRE) to U.K. health academic through AIMES Health Cloud Solution, Pivot3 announced
MoreA senior official at the Cybersecurity and Infrastructure Security Agency said CISA did not receive reports of any malicious cyber activity seeking to disrupt the 2020 presidential primary elections in 14 states,
MoreScott Rose, a computer scientist at the National Institute of Standards and Technology, told Federal News Network in an interview posted Tuesday that NIST’s Zero Trust Architecture Special Publication 800-207 seeks to
More